Frequently asked questions
Frequently asked questions
Below are answers to some of the questions that we’re most frequently asked. If you have any other questions about any aspect of My Council Services or working with Abavus please don’t hesitate to get in touch.
Payment gateway integration to My Council Services is done using our APIs (Application Programme Interface). We have successfully completed many payment integrations and we support all the major payment gateway providers. The most commonly requested and provided payment integrations are:
ADELANTE
BARCLAYCARD
CAPITA
CIVICA
GO CARDLESS
WORLDPAY
My Council Services provides a native mobile application option as part of its customer self service and mobile working suites. The mobile applications runn on the iOS, Android and Windows Operating Systems for a wide range of smartphones, tablets, iPads and Phablets with a uniform user interface.
Connection costs:
Access and use of the service by users when away from the office have no tangible cost implication for the Council. The only implication here is the data usage when users access the service from a device connected to the internet by a mobile (cellular) network, as opposed to wi-fi access. In this context the data plan for this device should be considered.
Since 2010 when we first introduced My Council Services, we have monitored and benchmarked data usage from 3G and 4G connected devices, there has been no discernible additional data consumption as a result of using My Council Services. Data usage in this scenario is entirely within usual ranges of tolerance.
Hardware costs:
Hardware provision (beyond the provision of the cloud infrastructure which is fully included) is not a facet of the relationship between Abavus and the Council. Hardware provision for remote devices and costs are a decision for the Council.
Abavus Ltd is registered with the UK Information Commissioners Office (ICO) under the registration numberZ2907810 as a data processor. Details here: https://ico.org.uk/ESDWebPages/Entry/Z2907810
All data held as part of held as part of the Council’s use of My Council Services remains the property of the Council. This ownership is contractually assured.
The data is used solely for the purpose of the Council carrying out its duties and in the delivery of its services.
All data in transit is encrypted. Any data at rest on a remote device is also encrypted.
The following security, encryption and key management protocols are in place:
The platform is designed and engineered to use ‘privacy by design and privacy by default’ principles, and latest standards and best practices will continue to be supported as the platform develops.
The following measures are in place to ensure the security of personal data that is stored and that may be transferred during planned and authorised workflow on the platform.
Firewall
The My Council Services database is never exposed beyond an internal firewall. The internal firewall technology is constantly reviewed and upgraded to the latest standards.
Penetration testing
Penetration tests are performed at least every 20 days. Any issues identified are immediately evaluated and acted upon. We also support third party penetration testing by Councils if they request this. The cost of such independent penetration testing will be borne by the Council. We also request that the Council share the full results of any independent penetration testing that it commissions, in order that we can act upon any relevant findings.
Source code encryption
All source code that is deployed to the My Council Services app is binary encrypted, preventing reverse engineering by hackers.
For Android devices specifically, the My Council Services native application can only be installed and run on the device’s internal memory.
Private key encryption
My Council Services utilises private key encryption technology to encrypt data packets. Private key encryption serves two purposes.
The first is authentication where the approach verifies the user.
The second is encryption of data. This approach assures that data in transit is secure and that it can only be accessed by an authenticated user upon receipt.
Secure sockets layer (SSL)
My Council Services uses Secure Sockets Layer (SSL) technology for all communication and web services. SSL is the standard security technology for establishing an encrypted link between a web server and a browser. This link ensures that all data passed between the web server and browsers remain private and secure.
Protecting against SQL injection
SQL injection is a code injection technique used to attack data-driven applications, in which malicious SQL statements are inserted into an entry field for execution (e.g. to dump the database contents to the attacker). My Council Services has best practice measures in place to prevent SQL injection, and regular testing is conducted after every version upgrade to protect against it.
Role-based access control (RBAC)
The extensive data security measures described here are layered over with RBAC via data roles which secure personal data, access and visibility to it.
Encryption standards
My Council Services offers a high level of encryption of data on any local device. The platform also protects against the possibility that Android native applications, if not adequately encrypted, can be reversed engineered for malicious reasons. To ensure that this cannot happen, the binary files are compressed, optimised, and obfuscated.
My Council Services uses AES 256 encryption web services for all mobile device communication. The My Council Services web services API can only be accessed via public access token using a unique identifier and is encrypted using AES256 encryption algorithm.
All transmitted data packets are also encrypted by private public key and further encapsulated by industry standard SSL layer providing very high levels of data security.
My Council Services uses transport layer security (TLS) 1.2 protocol for all communications. This ensures privacy and data security between our applications and our users on the internet.
Abavus takes practical measures to ensure that the actions of other customers on the My Council Services cloud platform will not impact on the quality of service for other users on the platform.
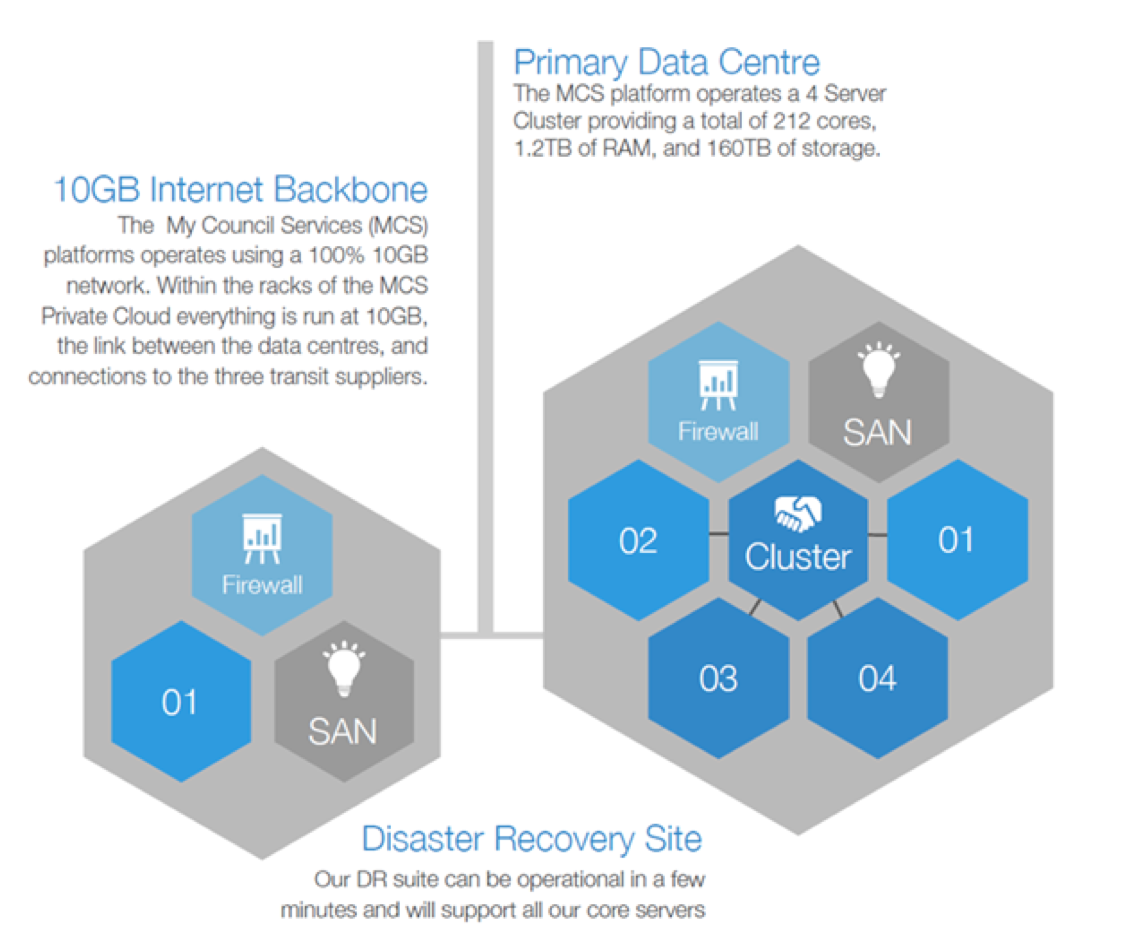
The My Council Services platform has been designed and engineered specifically for use by UK local government. There are many characteristics of its underpinning infrastructure that have been developed with this user community in mind. The schematics below provide an overview of some of the key infrastructure elements that guarantee a robust, high availability platform that is more than ready for the task of frontline public sector service delivery.
The hardware provision and the way this has been structured and deployed ensures, to the greatest extent possible, that the actions of one user will not negatively impact the quality of service for another user.
In particular we have chosen to provide the cloud hosting on private cloud infrastructure. The private cloud approach allows us to ensure that there is always sufficient processing, storage and connectivity provision to mitigate risks related to a user taking action that could skew resource allocation.
All hosting is based in the UK and we ensure 99.9% uptime, excellent performance, resilience and failover. Platform updates and improvements are all provided as part of the service.
The schematic below illustrates the high level architecture set up.
Beyond the hardware and infrastructure provision the user controls that are in place (through our RBAC module) allows the council to govern who can access which features and functions on the platform. This means that processes that could potentially create episodes of high resource demand can be corralled to only be accessible to the users that absolutely should have access to them.
Of course, there are certain external factors (for example regional internet disruption) that we are not able to mitigate against. We constantly monitor and assess these external factors.
No. Abavus does not share data with third parties or across other services.
All data that is stored and processed on the My Council Services platform is hosted and processed in the UK.
Both the primary and secondary hosting facilities are physically located in the UK. Customers can, by prior arrangement, make an accompanied visit to these facilities if desired.
The rights and freedoms of data subjects are fully protected in line with the General Data Protection Regulations (GDPR) with which Abavus and the cloud services it provides is fully compliant.
More details on the specific safeguards that are in place can be reviewed on our website at the following link:
Click here for details on how My Council Services supports the GDPR
Click here for the Abavus Ltd Privacy Policy
My Council Services is a cloud-based platform and the entire infrastructure and all data is securely hosted and stored in the UK.
Our primary data centre is provision by Redcentric (https://www.redcentricplc.com/ ) and is accredited through ISO27001.
The Telehouse London Data Centres, provide our secondary data centre (https://www.telehouse.net/london-data-centres )and adhere to the following internationally recognised accreditations:
- ISO/IEC 27001:2013 (Information Security Management)
- ISO 22301:2012 (Business Continuity Management)
- PCI-DSS v3 (Payment Card Industry Data Security Standard)
- ISO 9001:2008 (Quality Management system)
- ISO 14001:2004 (Environmental Management)
- ISO 50001:2011 (Energy Management)
- BS OHSAS 18001:2007 (Occupational Health and Safety Management)
- RMADS (Public Sector Compliance)
Abavus is registered on the Government Digital Market Place (G Cloud 10).
You can access our products and services listings at the following links:
